- Succinct just launched ZCAM, a free iPhone app that signs photos and videos inside the Secure Enclave the moment you capture them.
- Any edit — human or AI — breaks the signature.
- Here's how it works and why it matters in a year when 7 commercial AI detectors lose up to 96% accuracy against trivial edits.
TL;DR
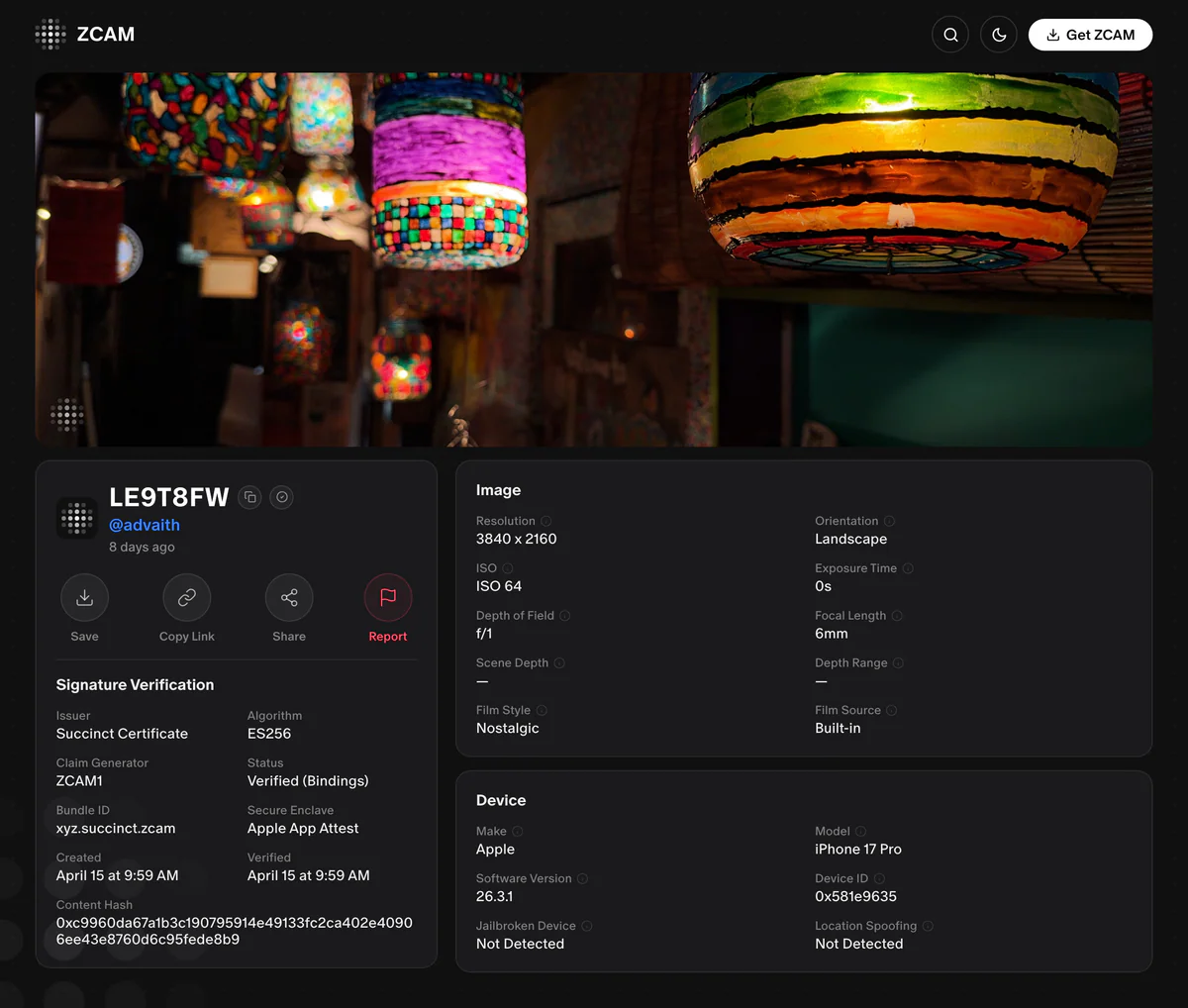
Succinct — the applied cryptography lab behind the SP1 zero-knowledge virtual machine — just launched ZCAM, a free iPhone app that cryptographically signs every photo and video at the moment of capture. The signature lives inside Apple's Secure Enclave, is bound to the ZCAM app via Apple App Attest, and is embedded in the file as a C2PA manifest. Anyone, anywhere, can verify a ZCAM image at zcam.succinct.xyz — and if a single pixel changes, the signature breaks.

What's new
On April 23, 2026, Succinct shipped its first consumer product. ZCAM is available now on the iOS App Store as a free download, and an open-source reference SDK has been published at github.com/succinctlabs/zcam1-sdk. You can try a live verified photo here: zcam.succinct.xyz/z/LE9T8FW.
The pitch is simple and direct: instead of trying to detect AI-generated media after the fact, prove your media is real at the source, using the same class of hardware cryptography that already guards Apple Pay and passkeys.
Why it matters
Succinct benchmarked 7 commercial AI image detectors against a simulated fraud pipeline. Trivial post-processing — blur, recompression, a sprinkle of noise — dropped detection rates by up to 96%.
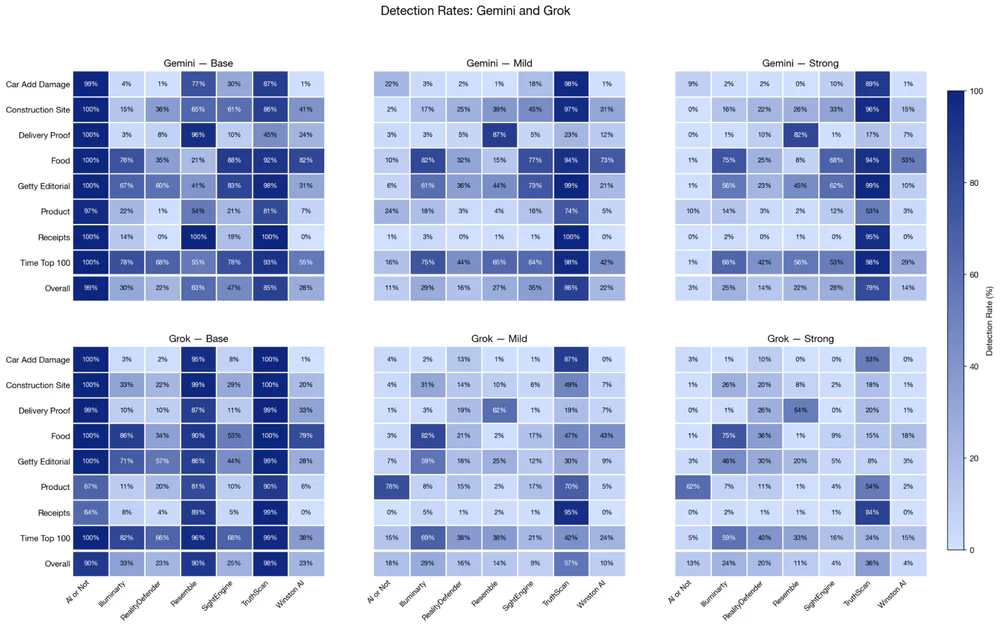
That is the gap ZCAM closes. A cryptographic signature is binary — it either verifies against the device's attested key or it doesn't. There is no 73% confidence score for a hash mismatch.
Technical facts
Here is what actually happens when you tap the shutter in ZCAM:
- The raw pixel bytes of the photo (or frame sequence for video) are hashed.
- The hash is sent to the iPhone's Secure Enclave, which signs it with a device-unique private key that never leaves the hardware.
- Apple's App Attest service produces an attestation chain binding that key to the ZCAM binary on a genuine, unmodified iPhone.
- Signature + attestation + capture metadata are packaged as a C2PA manifest (the open standard backed by Adobe, Microsoft, Google, OpenAI, and the BBC) and embedded in the output file.
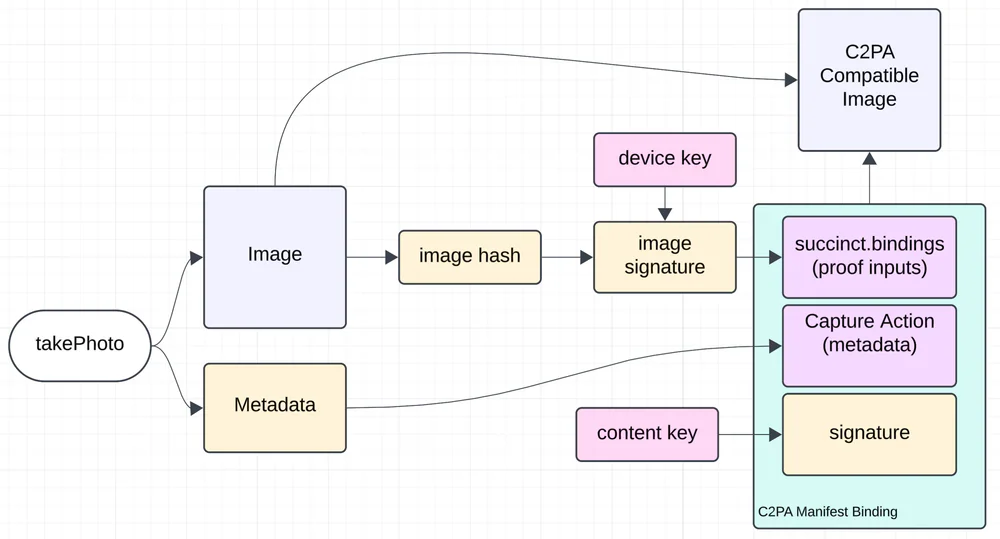
Verification is the inverse: extract the manifest, recompute the hash from the pixels you see, check the signature against the App Attest chain. Change one pixel — crop, filter, re-save in Photoshop, run it through any AI tool — and the recomputed hash no longer matches. The image is still viewable; it just can no longer claim to be a verified ZCAM original.
Under the hood, ZCAM is a showcase for the cryptographic stack Succinct already runs in production: the SP1 zkVM — described by the company as the world's fastest zero-knowledge virtual machine — currently secures over $4B in digital assets and is used by Google Quantum AI, Polygon, Optimism, and Celestia.
Comparison
| Approach | Root of trust | Hardware cost | Survives edits? |
|---|---|---|---|
| AI detectors (Hive, Optic) | Probabilistic model | Free | No — up to 96% accuracy drop |
| Adobe Content Credentials (desktop) | Software signing | Free | Easily stripped |
| Sony / Leica / Nikon C2PA cameras | In-camera secure chip | $3K+ body | Yes, binary |
| ZCAM | iPhone Secure Enclave + App Attest | Phone you already own | Yes, binary |
Use cases
- Journalism and conflict reporting — prove a photo wasn't staged or deepfaked, straight from a reporter's phone.
- Insurance claims — damage photos arrive with a verifiable timestamp and device origin.
- Marketplace and real estate listings — prove the listing photo is the real item, not a stock render.
- Legal evidence — a cryptographic chain of custody from shutter to courtroom.
- Public figures and creators — a way to counter the now-routine "that's AI-generated" denial of real footage.
Limitations & pricing
ZCAM is free. The honest caveats, which Succinct itself leads with:
- iOS only at launch — the app relies on Apple Secure Enclave + App Attest. No Android date announced.
- The open-source SDK is unaudited and explicitly marked not production-ready.
- Secure Enclaves are strong but not theoretically perfect — prior generations have been broken, and middleware between sensor and enclave remains a theoretical attack surface.
- ZCAM proves provenance, not truth. A real photo of a staged scene still verifies. Cryptography cannot tell you whether the thing in front of the lens is honest — only that the lens, sensor, and file are.
What's next
Succinct is framing ZCAM as an "important first step" in a broader Prove What's Real product line — applied cryptography pulled out of the crypto-assets sandbox and into the mainstream internet. Expect more C2PA-powered primitives, SDKs for third-party camera apps, and eventually Android once an equivalent attestation pipeline is in place.
If you have an iPhone, the experiment is one tap away. Shoot a photo in ZCAM, drop the file into zcam.succinct.xyz, and watch it verify against a device you literally just held.
Nguồn: blog.succinct.xyz, succinct.xyz, ZCAM SDK.



