- SSH Remote Port Forwarding (-R) dao nguoc luong traffic so voi local forwarding: SSH daemon tren remote server mo port moi va gui traffic nguoc ve local machine qua tunnel ma hoa.
- GatewayPorts yes la bat buoc neu muon expose public - mac dinh tunnel chi bind vao localhost cua remote server.
- Mot lenh don gian ssh -R bypass duoc NAT, firewall, va expose toan bo private network qua bastion host.
TL;DR
SSH Remote Port Forwarding (-R) la phuong phap nguoc: thay vi mo port tren may cua ban de ket noi ra ngoai (local forwarding), no mo port tren remote server va gui traffic nguoc ve may ban. Huu ich khi may ban nam sau NAT, firewall, hoac khong co public IP.
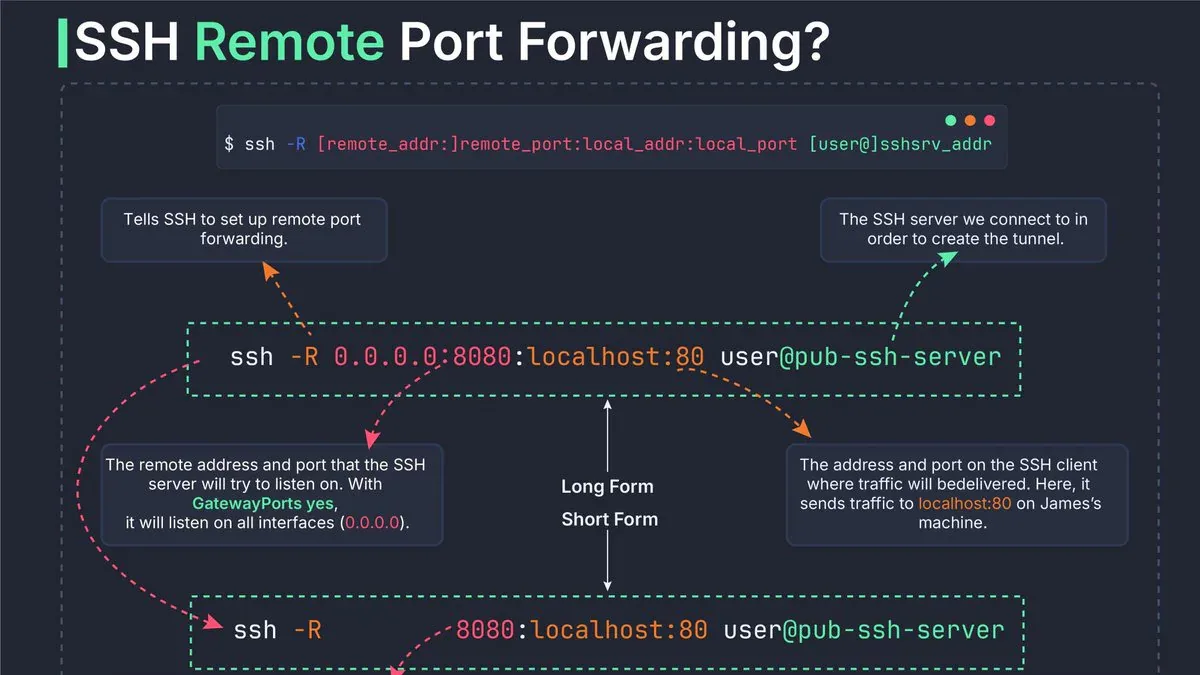
ssh -N -R remote_port:local_addr:local_port user@public-ssh-serverCo che hoat dong
Khi chay lenh ssh -R, SSH daemon tren remote server (sshd) bat dau lang nghe tren mot port moi. Moi ket noi den port do se duoc chuyen nguoc qua tunnel SSH da ma hoa ve may local cua ban.
Luong traffic cu the:
- May local (SSH client) tao ket noi SSH ma hoa toi remote server
sshdtren remote server mo port lang nghe moi (do-Rchi dinh)- Client ben ngoai ket noi toi port nay tren remote server
sshdchuyen traffic nay nguoc qua tunnel ve may local- SSH client giao traffic toi port dich cuc bo (dev server, DB, v.v.)
Meo ghi nho:
ssh -L local:remote- L mo port tren localssh -R remote:local- R mo port tren remote- Luon la ve trai cua dau hai cham mo port lang nghe moi
GatewayPorts - Bay an quan trong
Day la dieu ma nhieu nguoi bi vap: mac dinh, tunnel -R chi bind vao localhost cua remote server. Nghia la chi nguoi dang o trong remote server moi truy cap duoc - khong phai internet ben ngoai.
De expose public, can them vao /etc/ssh/sshd_config tren remote server:
GatewayPorts yesSau do restart sshd. Voi GatewayPorts clientspecified, ban co the chi dinh chinh xac dia chi bind bang cach them IP vao lenh -R:
ssh -R 0.0.0.0:8080:localhost:80 user@pub-ssh-serverCac truong hop thuc te
1. Chia se dev server khong can deploy
ssh -R 8080:localhost:5534 user@ssh.server.comClient truy cap ssh.server.com:8080 se thay duoc app dang chay o port 5534 tren may ban.
2. Reverse SSH - vuot firewall chan port 22
# Tren may bi chan:
ssh -R 2200:localhost:22 ubuntu@18.170.229.50
# Tren remote server, SSH nguoc ve:
ssh -p 2200 andrew@localhost3. MySQL tunneling toi may co mang rieng
ssh -R 3306:172.31.46.48:3306 ubuntu@18.133.180.232
mysql -h 127.0.0.1 -P 3306 -u root -p4. APT cho server bi cam internet
ssh -R 8080:eu-west-2.ec2.archive.ubuntu.com:80 ubuntu@172.31.46.48Them vao /etc/apt/apt.conf.d/01proxy:
Acquire::http::Proxy "http://localhost:8080"5. Bastion host mode - expose ca private network
Khong chi gioi han o localhost cua may ban - ban co the expose bat ky may nao trong mang noi bo:
ssh -R 8080:192.168.1.100:80 user@pub-serverDay la use-case huu ich cho dev lam viec tren home lab: dung laptop mong (thin client) lam cau noi, expose may chu phat trien o nha qua ingress gateway.
Chay ngam va tips
De giu terminal khong bi chiem:
ssh -f -N -R 8080:localhost:3000 user@server.com-f: Chay background ngay sau khi xac thuc-N: Khong mo remote shell, chi tunnel- De kill: dung
ps aux | grep sshtim PID roikill <PID> - Windows: dung
127.0.0.1thay vilocalhost(tranh loi IPv6)
Bao mat khi dung remote forwarding
Remote port forwarding mo cua cho ket noi den - can chu y:
- Chi forward port can thiet - moi port them la mot attack surface moi
- Tat password auth, dung SSH key pair
- Han che GatewayPorts theo IP cu the khi co the (
GatewayPorts clientspecified) - Ket hop fail2ban chong brute force
- Monitor active connections:
netstat -tlnp | grep sshd - Giu SSH client/server luon update
Neu SSH connection bi ngat, moi service forward qua tunnel se mat ket noi ngay - day la diem yeu chinh so voi cac giai phap managed nhu Cloudflare Tunnel hay Tailscale.
So sanh nhanh
| Tinh nang | Local (-L) | Remote (-R) | Dynamic (-D) |
|---|---|---|---|
| Port mo boi | SSH client (local) | SSH daemon (remote) | SSH client (local) |
| Huong traffic | Local - Remote | Remote - Local | Linh hoat (SOCKS) |
| Use case chinh | Truy cap DB noi bo | Expose dev server | Secure browsing |
| Can GatewayPorts | Khong | Co (de expose public) | Khong |
Ket
Remote port forwarding la ky thuat zero-dependency manh me nhat de vuot NAT va expose service cuc bo ma khong can infrastructure phuc tap. Hieu duoc 3 flag co ban - -L, -R, -D - va meo "canh trai mo port moi" la du de xu ly 90% truong hop SSH tunneling trong thuc te.
Nguon: sysxplore - SSH Tunnels Deep Dive Part 2, iximiuz - A Visual Guide to SSH Tunnels, datawookie.



